Branch’s products influence a wide variety of roles and teams within companies around the world. The most successful organizations have teams of users across the product, marketing and engineering departments working jointly on their Branch applications. To enable this collaboration a need for controlling and managing access arises. For instance, it may not make sense for a marketing analyst to reconfigure your iOS deep linking settings. On the other hand, you may not want to expose sensitive private key information to a summer software development intern. Regardless of the size of your organization, giving appropriate permissions to your company stakeholders that use Branch can help mitigate security, privacy, and data reporting concerns, and can reduce risks associated with unintended changes.
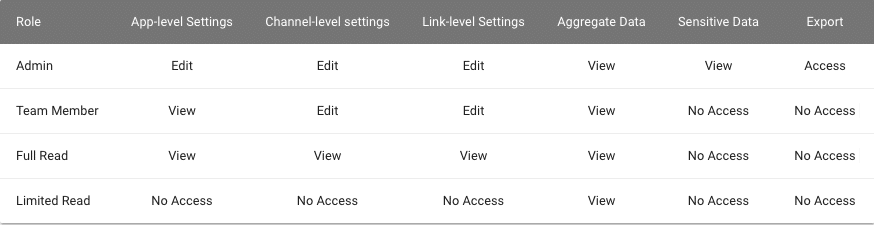
Branch recently launched an improved version of user-level access control. This release gives admins the power to grant users permissions from a list of six categories: App-Level Settings, Channel-Level Settings, Link-Level Settings, Aggregate Data, Sensitive Data, and Export. These six categories are derived from the principle of least privilege, which are the trademarks of information security best practices.
App-level Settings
Granting a user these permissions will provide them access to settings or features that can impact functionality across your entire app. This level of permission exists for those who need to control and view the account settings, including app settings, billing, team info, and SDK set-up.
Channel-level Settings
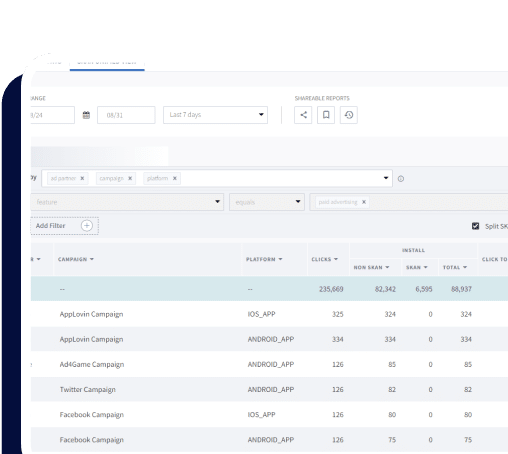
These permissions pertain to the specific marketing channels for which you use Branch, including Journeys, ads, emails, and more. A user with these permissions is likely to be involved in setting up marketing campaigns and/or exporting data.
Link-level Settings
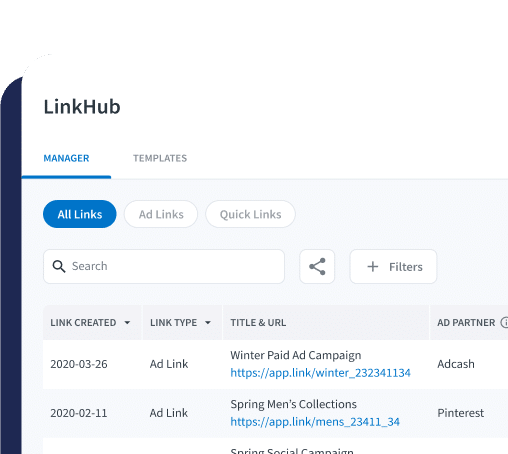
A user with link-level settings permissions will be able to configure link data and settings on a per link basis. This is not to be confused with configuring link settings at an app level. This user will typically create and edit links for different campaigns.
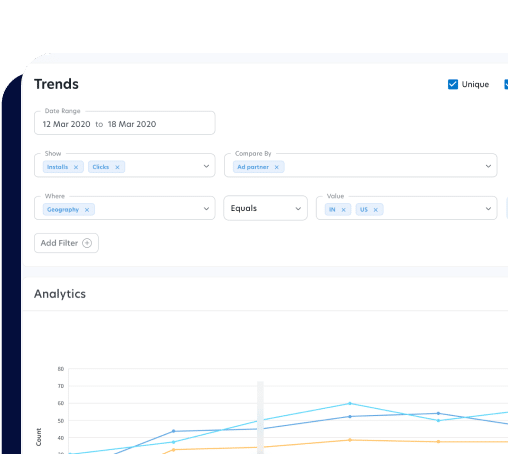
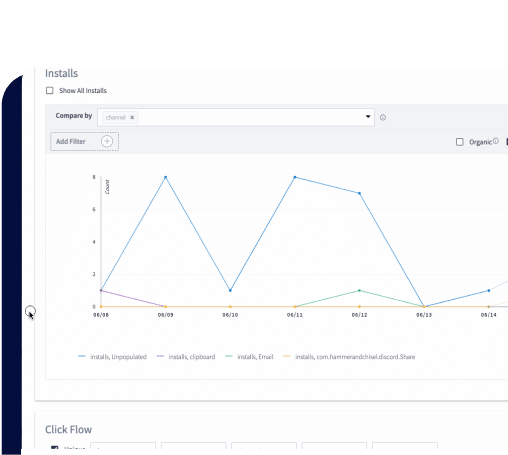
Aggregate Data
This permission limits users to only visualize the Branch data from a high level. These users cannot see granular user information. This should be the access level of users who do not have a specific reason for seeing individual user information. This provides a level of data privacy that may be useful for data regulations like GDPR.
Sensitive Data
This permission category should be reserved for a select group of individuals that can be trusted with user-identifying, payment-related, or secret information (e.g. Branch Key and Secret).
Export
This permission allows users to export sensitive data from pages to which they have been granted access. This should be limited to users who have specific needs for pulling data out of the dashboard for their own usage.
Access Roles
Within each set of permissions, you can specify a given user’s level of control. We provide several default profiles with predefined access levels. These default profiles, along with their corresponding permissions, are below:
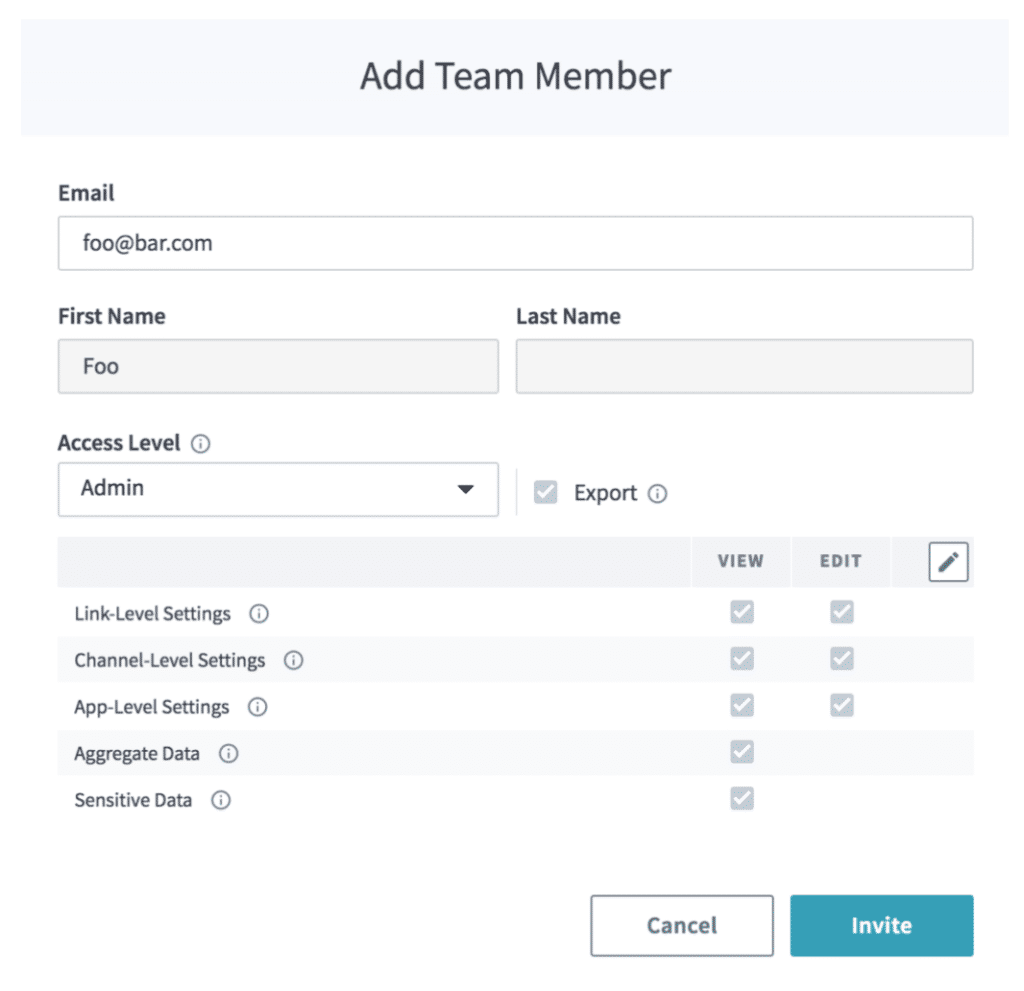
If none of these configurations work for a particular user, we also offer the option of creating custom roles to give you as much flexibility as possible when assigning access. When adding a new team member, you will be presented with a modal that allows you to select a default profile from a dropdown; if you select the Custom profile from the dropdown, you will have full control over which permissions a user has and does not have.
The Importance of User Controls
Although it may seem unnecessary to establish certain access controls when your Branch team consists of only a few users, scaling out a team with a well-defined structure and hierarchy can bring peace of mind to your organization. When introducing new users to your team, you should always grant them with the lowest level of permissions possible to their jobs. As they progress in their involvement, continue to roll out features gradually. It is much easier to grant permissions to someone than take them away.
Branch is, inherently, a multi-organization tool. There are engineering roles that will never need to touch marketing features, and vice versa. If users have permissions that are specific to their role, it is impossible to step on the toes other organizations.
The earlier you establish your rules and structure, the easier it will be to scale Branch within your company while continuing to keep a peace of mind. It’s always better to be safe than sorry.