Are we still talking about fraud?
Yes. Ad fraud follows dollars, and looking at the accelerated growth that the mobile industry has seen over the past few years, it’s easy to see why fraudulent companies are drawn to this industry. As ad spend increases, so does ad fraud. Brands are forecasted to spend $77 billion on mobile in-app advertising this year, and about $26.5 billion will be lost to mobile in-app fraud.
Particularly at this time of the year, when many marketers are ramping up their efforts to drive holiday sales, the cost of ad fraud is not just the cost of wasted media spend, but also the cost of missed opportunities.
For this reason, Jampp and Branch teamed up to share some practical tips for identifying different types of fraud and best practices advertisers should keep in mind.
Is it poor performance or is there something else going on?
The best way to understand the different types of ad fraud is to consider that they are directly linked to the pricing model in place.
The more competitive the markets get, the more pressure on app advertisers to deliver growth. User acquisition managers are constantly striving to get the largest possible amount of new users at the lowest possible cost. While many say their KPIs are based on lifetime user value and in-app events, there is still a large part of the industry (and investors who support it) that avidly watches “market-share” and download counts as success metrics, which is why the CPI model persists.
Now let’s take a look at five different types of ad fraud and the red flags advertisers should look out for
Click Spamming
Click spamming, also referred to as click flooding, consists of fake click requests. Fraud companies extract real campaign URL tokens for a specific device type or location. They then execute programs to generate a high volume of click requests, randomizing device-IDs and user agents at each iteration. The Goal: to randomly get attributed installs/events.
- What to look for High CTR with low CVR.
- What to do: Check for click-to-install time delta over a time window of a few days. While there may be exceptions, in healthy campaigns there should be a sharper “fall” of installs vs clicks over time (as shown on the graph on the left). If the number of installs is sustained for a longer time window, it may indicate fraudulent activity.
Click Injection
Fraud companies, through previously gained access to the user’s mobile device, detect when a new app is being installed and at that precise moment fire a click to gain the attribution.
This type of fraud is generally driven by a few sites which have generated the click in order to claim high performance.
- What to look for High CTR with very high CVR
- What to do: Check click-to-install time delta over a short time window (seconds). More often than not, a healthy campaign will show few to no installs in the first seconds after the click (as seen in the graph on the left), given that it takes some time to go to the app store, download the app, and open it. If there’s a sudden spike in installs in the first few seconds (or milliseconds) after the click, it likely constitutes an indicator of suspicious activity.
Pixel Stuffing
Pixel Stuffing, or ad stacking, refers to the process of serving one or multiple ads in a single 1X1 pixel frame. This makes the ads humanly unviewable, and as a consequence advertisers pay for impressions that won’t convert.
- What to look for High impressions with low CTR (and low CVR)
- What to do: Demand impression-level transparency. The easiest way to catch this type of fraud is to have a clear view of how each placement is performing. If you are optimizing towards in-app events, the optimization itself should naturally cut these publishers off.
The above-mentioned examples have been around for a while, and the flags and subsequent analysis are pretty clear cut. However, fraud is not a static thing, it is constantly evolving. Lately, more elaborate schemes have surfaced, like Malicious Apps or Malware, as well as certain types of Spoofing.
Domain Spoofing
This is a type of spoofing where the impression and the user are real but the bundle ID, which is the identifier of the app, is not.
The bundle ID allows the fraudulent app to disguise itself as a premium app. In this way, the fraudulent app will charge premium fares for low-quality placements. Spoofing could also be found on other variables such as location or Device ID.
Malware or Malicious Apps
Malware is a piece of software that disrupts a device to damage it or to collect data without users’ consent, committing fraud or tracking user behavior. It is usually triggered by clicking on suspicious links or downloads, and can take the form of viruses, bots, spyware, or adware among others.
For these types of fraud, there is little that advertisers can do on their end, but if the pricing model places the incentive on real events and real revenue, optimization and predictive media buying models will automatically stop bidding for the fraudulent inventory. Working with partners like Jampp that employ advanced global blacklists, that are constantly revised and updated, is another barrier of defense against these types of fraud.
Wrapping Up: 5 keys to fighting mobile ad fraud
There are multiple variables that make the mobile industry an ideal scenario for fraudsters, but it’s not a lost battle. Marketers looking to safeguard their ad spend against ad fraud can implement the following measures:
- Don’t hate the player, hate the game: Understand that your pricing model determines where the incentive is for your supply partners. Pay attention to what’s happening from the first impression to the last event. Be prepared for a “rude awakening” as LetGo’s Mobile Acquisition Director, Adrian Sarasa, calls it: “app marketers that make the move to programmatic often get a rude awakening when they see their actual success metrics (…) You need to be aware that your [cost per action] or whatever KPI you’re looking at will be different than it was before, but the good thing is that it will also be more real.” Be wary of companies who charge on a CPI or CPA basis, because there is a high incentive to buy the cheapest traffic available and cannibalize organics.
- Demand Transparency: There is no reason for a supply partner not to share impression-level data. Running on programmatic gives you and your partners the visibility needed to take proactive and preventive measures. Jampp uses historical data to ensure we only bid and serve impressions to real users; and block bids from fraudulent traffic signals such as blank or bad formatted device IDs, publishers with suspiciously high bid request frequencies, and/or invalid source of publisher app bundle.
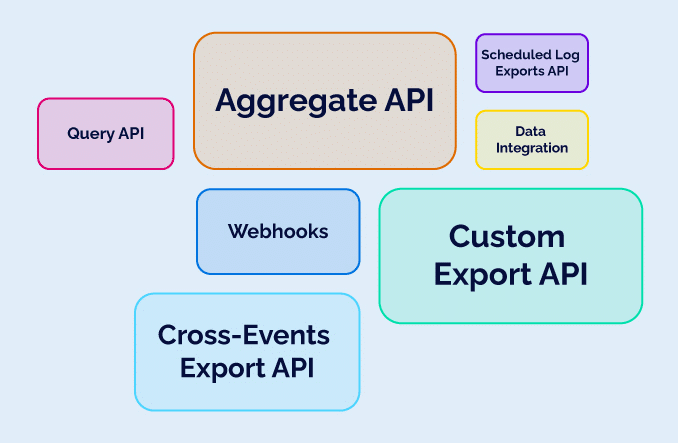
- Know what to look out for: Bad performance is sometimes just bad performance, but as the examples above show, there are certain flags for suspicious activity if you know what to look for. Branch’s cross-platform infrastructure provides unique insights into fraudulent behavior by incorporating data signals, allowing the detection of new kinds of fraud. Branch’s predictive modeling algorithm enables the identification of extremely unnatural browser behavior to then use this information to trigger “predictive modeling fraud” blocking.
- Find the right tools and partners: As we always run and optimize campaigns towards a real ROI or real user engagement target that is measured in-app, the mere process of optimization takes care to naturally cut and penalize any potential fraudulent activity. Blacklisting and whitelisting publishers, removing suspicious device IDs from audiences, applying automatic bid price prediction from non-performing variables are some of the measures we take to ensure we are actively cutting any type of suspicious activity.
- Be vocal in the industry: Ad fraud has been a recurring topic in conferences and happy hour conversations since… probably the birth of mobile marketing, but it’s important to continue having these conversations. As anti-fraud technology evolves, so does ad fraud. As long as there are companies willing to work with them, fraudulent supply partners will continue to exist.
Moving forward ➡️
Earlier this year, Branch launched the Branch Certified Partner Program. To become Certified by Branch, all partners must meet higher technical requirements, including passing secondary publisher data, as well as sharing campaign, ad name, and device ID.
Jampp eagerly joined the initiative to collaborate with Branch on its ongoing efforts to fight mobile ad fraud by agreeing to common definitions for what constitutes fraud and sending secondary publisher and device ID for in-app traffic.
About Jampp
Jampp is the programmatic platform of choice for the fastest growing on-demand companies worldwide. We unlock programmatic advertising to drive incremental growth.